- Home
-
Solutions
-
Talent Development Platform - Base
-
Engagement Survey
-
Bullseye Survey
-
Succession Planning
-
AI Coach
-
AI Advisor
-
Compensation Planning
-
Talent Match
-
Ethics Lifeline
-
Workforce Planning
-
Executive / Human Capital BI Dashboard
-
Operational BI Dashboards
-
Bullseye OKRs
-
Training Management
-
Competency Management
-
Performance Management
-
Recognition & Rewards
Talent Development - Base System
The Bullseye platform is modular, meaning you generally only need to pay for the solutions you need today. Subscribe to one or all of our solutions depending on what your organization needs now.
Key Features
- Employee Profile
- Performance Reviews, Peers, and 360s
- Action Plans
- Talent Development Plans
- Stay and Exit Interviews
- Check-ins
- Bullseye Teams
- At-a-Glance Dashboard
Learn More
Engagement Survey
The degree to which an employee feels passionate about their work and committed to an organization can be measured as Employee Engagement. It is a key factor in the success of a business or organization as it is closely correlated with profitability, productivity, safety, absenteeism and turnover.
Key Features
- Automated pulse surveys
- AI-powered sentiment insights
- Results may be filtered by any demographic designator
- Privilege-based access to survey results
- Anonymous and non-anonymous surveys
- Research-backed question bank and survey templates
- Engagement reporting and analytics
Learn More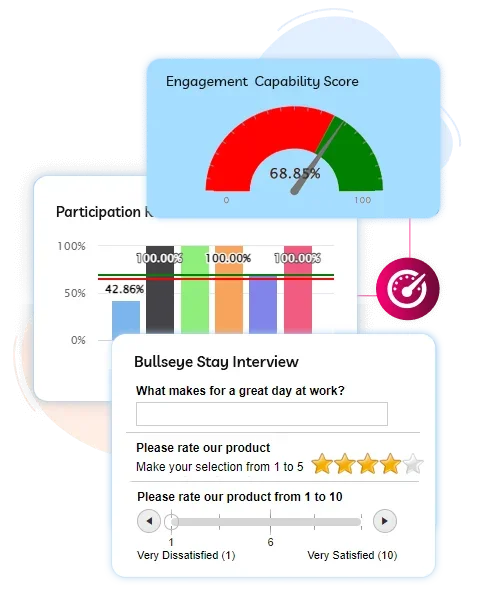
Bullseye Survey
Key Features
- Surveys can be custom-branded, with fully configurable directions and messaging
- Multiple survey campaigns may run concurrently
- Surveys can be anonymous or non-anonymous
- There are a wide range of survey formats, including free emoji responses
- Access the analytics through survey Dashboards
- AI assisted summary of open-end text responses
- Survey can be deployed through e-mail or QR code
- Survey questions and formats are easily configurable by clients
- Results are compiled in real-time, providing immediate feedback from constituencies
- Results may be filtered by any demographic designator or exported for further data manipulation
- Access to survey results is privilege-based
Learn More
Succession Planning
Our Succession Planning Software is designed to be your strategic ally in grooming and developing talent within your organization. By identifying potential leaders, nurturing their skills, and preparing them for key roles, you can ensure a seamless transition when the time comes. With BullseyeEngagement, you're not just planning for succession; you're actively shaping the future of your organization.
Key Features
- Identify Critical position
- Interactive Talent Matrix (9 Box)
- Risk Assessment
- Identify succession candidates using Talent Match and job competencies
- Position Succession Profiles
- Succession Charting
- Individual Development Plans
- Organization Succession Analytics
Learn More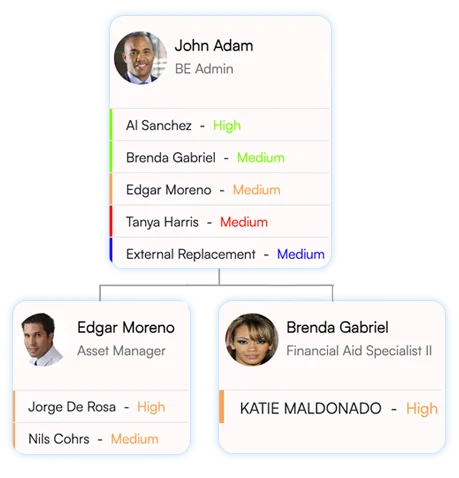
AI Coach
Real-time coaching that helps managers lead better in the moments that matter. AI Coach turns people's insight into practical guidance for feedback, conflict, goal conversations, and employee development. It is designed to drive follow-through, not just measurement.
Key Features
- Conversation guidance tailored to each individual, grounded in personality and motivation insight
- In-the-moment coaching for feedback, expectations, and performance conversations
- Early friction detection with practical resolution paths before escalation
- Coaching support that helps new managers build confidence faster
- Bias-aware prompts that improve consistency and decision quality
- Development guidance that makes growth conversations easier to deliver
Learn More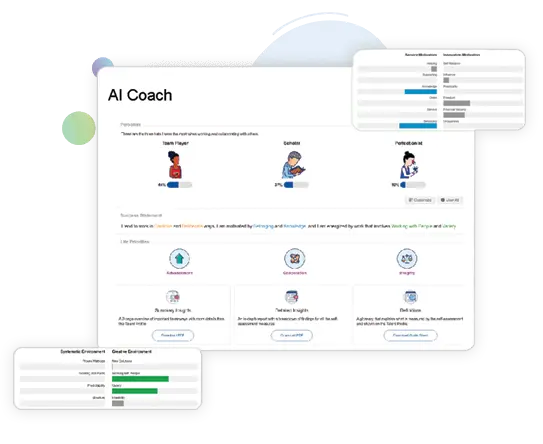
AI Advisor
Real-time insights into succession risks and coverage for critical positions—so leaders can act accordingly and plan with confidence.
AI Advisor analyzes signals across Bullseye modules, surfaces what matters most, and produces leadership-ready guidance and action plans. It helps leaders move faster with defensible decisions that are easier to communicate and track.
Key Features
- Identifies critical roles and succession risks automatically
- Measures bench depth and succession coverage
- Ranks best-fit successors
- Calculates readiness timelines
- Builds individualized development plans automatically
- Delivers a clear, actionable plan
Learn More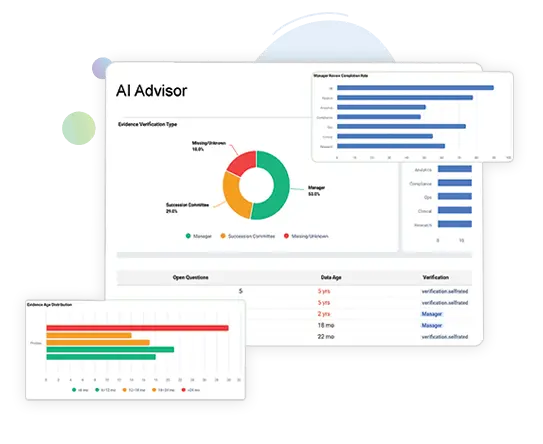
Compensation Planning
Staying one step ahead is easy with BullseyeEngagement's Compensation Planning tool.
Key Features
- Include salary and bonus compensation cycles
- Performance and talent based compensation adjustments
- Bonus plan payout and one-time bonus awards
- Customer specific pay adjustment guidelines
- Compensation adjustments measured against budgets
- Automatic calculation into local currencies
- Benchmarking data
- Gender pay equity analytics
- Configurable workflow approval process
- Post-cycle employee compensation statements
- HRIS Integrations
Learn More
Talent Match
BullseyeEngagement's Talent Match Feature can help to remove the guesswork from the process. This feature allows you to create a profile of your preferred candidate and matching that against the available internal candidates based on your customized criteria.
Key Features
- Identify and rank "best-fit" internal & external candidates for open positions based on employee profile characteristics
- Identify potential successor candidates for succession planning initiatives
- Include contractors, alumni, or non-employees in searches
- Assemble project teams with employees from various offices and locations based on position criteria
Learn More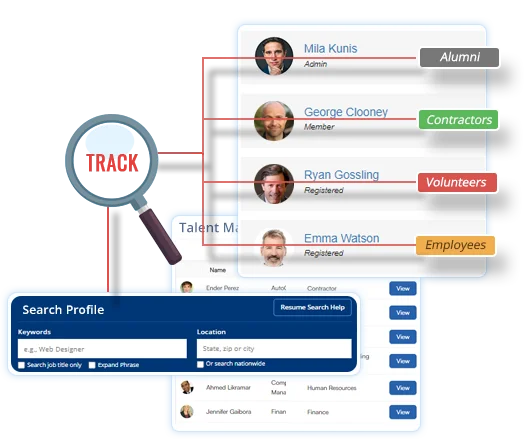
Ethics Lifeline
Having a tool such as the Ethics Lifeline increases the likelihood that employees will actually speak up about critical issues that put your organization at risk.
Key Features
- Allows for employees to create truly anonymous reports of questionable behavior
- Leadership may create action plans to investigate and report on complaints
- Generate reports of complaints handled and their resolution
- Direct employee complaints to designated recipients based on the topic reported
- Leadership can communicate to the organization on any reported complaints
Learn More
Workforce Planning
The Workforce Planning Module from BullseyeEngagement is here to help you to prepare for the future by consolidating your workforce planning. It puts all of your relevant information in one place so you don't need to rely on excel spreadsheets, sticky notes, paper and powerpoints to make workforce planning decisions. The Workforce Planning Module makes it easy to plan for restructuring or reductions in force, and project future budgetary and recruiting needs.
Key Features
- Modeling tool to create pro forma organization charts
- Estimate cost effects of staff reduction or business expansion initiatives
- Comparative organizational charts for multiple scenarios
- Replace spreadsheets to improve collaboration and information sharing
Learn More
Leadership Human Capital BI Dashboard
BullseyeEngagement's Executive/Human Capital BI Dashboard interface gives you key data right at your fingertips, allowing you to easily assess the health of your organization, quickly course-correct when issues arise, and make better informed decisions
Key Features
- Calculate and display 70+ KPIs as recommended by the SHRM (Society for Human Resource Management) and the ISO (International Organization Standardization)
- Easy configurability to add to or delete metrics from the standard Dashboard
- Optional benchmarking to industry averages or to internal targets
- Drilldown to successive levels of details
- Simple methodology to populate data in the Dashboard
- User-controlled privileged access to elements of the Dashboard
Learn More
Business Intelligence Dashboards
Having instant access to all of the information that you need to make informed decisions about your business is invaluable. With BullseyeEngagement's custom-developed business intelligence dashboards, you have real-time access to the key organizational performance metrics you need right when you need them.
Key Features
- Design turnkey business intelligence (BI) dashboard to customer specifications
- Measure business results against targets or thresholds
- Drilldown to successive levels of details
- Use action planning to assign follow-up responsibilities
- Customizable data visualization
- Notification alerts and reminders
- Update data based on customer determined frequency
- Simple methodology to populate data in the Dashboard
- User-controlled privileged access to elements of the Dashboard
Learn More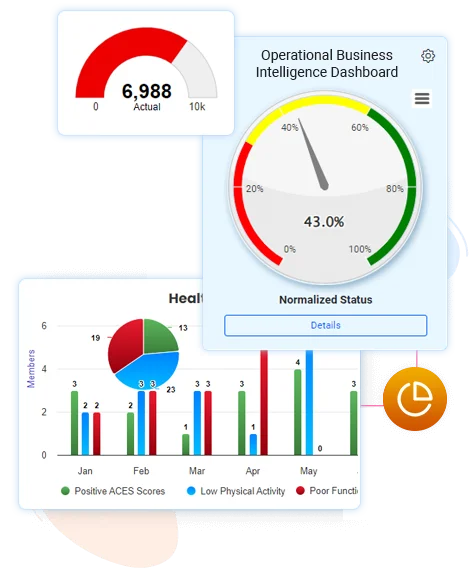
Objectives & Key Results
OKRs stand for "Objectives and Key Results." It is a collaborative goal-setting methodology used by teams and individuals to set challenging, ambitious goals with measurable results.
Key Features
- Interactive goal setting with measurable milestones
- Manager can override auto rating with explanatory comments
- Task tracking of steps to achieve key results
- Associate library of competencies to development objectives
- Includes chat features to facilitate real time collaboration
- Automated performance rating based on successful completion of goals or key results
- Robust reporting tools for OKRs completion status
Learn More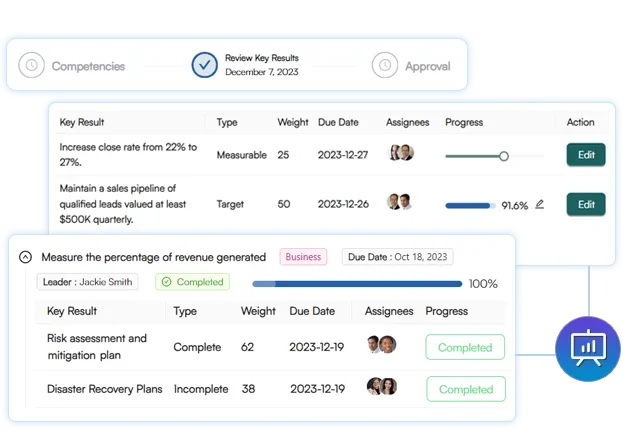
Training Management
BullseyeEngagement's Training Management Software solution tracks the progress of employee training programs. Whether the content is internally developed or the product of a third-party Learning Management System, BullseyeEngagement keeps track of employee progress on training. By keeping track of learning and training progress in a single interface, BullseyeEngagement provides managers and HR leaders greater insight into the overall development of individual employees and the organization as a whole.
Key Features
- Access to centralized training library
- Monitor training progress through At-a-glance Dashboard
- Interface with learning management systems (LMS)
- Set up prerequisites to training courses
- Ability to request learning courses
- Assign and track trainings individually or in bulk
Learn More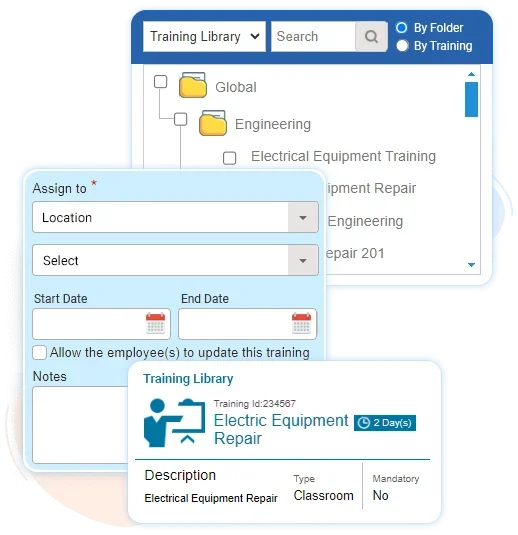
Competency Management
Competency Management is an investment in the development of your employees and the long-term success of your organization. Understanding the individuals that you have working for you, their strengths, weaknesses, and areas where they can best grow & develop to best serve the company will go a long way in creating a workplace that is not only productive, but a place where people want to work.
Key Features
- Create or import a library of job competencies
- Set target levels of competencies for job roles
- Enable competencies assessment by both manager and employees
- Allows employees to see other job roles that are consistent with their competency levels
- Enables communication between manager and employee regarding respective assessments
- Track competency development over employee's career
- Identify job skill gaps based on competency assessment
- Robust reports of skills gaps and surpluses
Learn More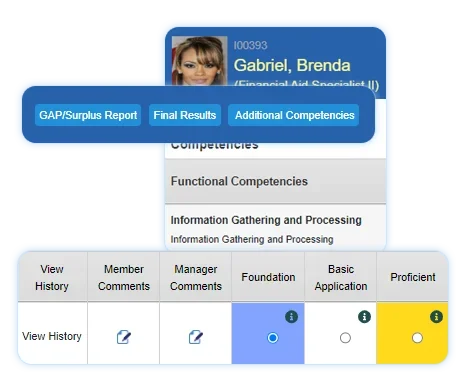
Performance Management
Bullseye's appraisals can be configured according to your current management culture/business cycle and are simple to use.
Key Features
- Available range of appraisal formats: manager, self, peer, team and 360 reviews
- Fully configurable appraisal criteria and choice of rating and weighting scales
- Integrate performance goals to appraisal criteria
- Scheduled and on-demand reviews
- Auto assign appraisal based on hire date, probationary date or other specified date
- Configurable email notification system for reminders
- Configure workflows to the customer's specific approval process
- Configurable employee appraisal report
Learn More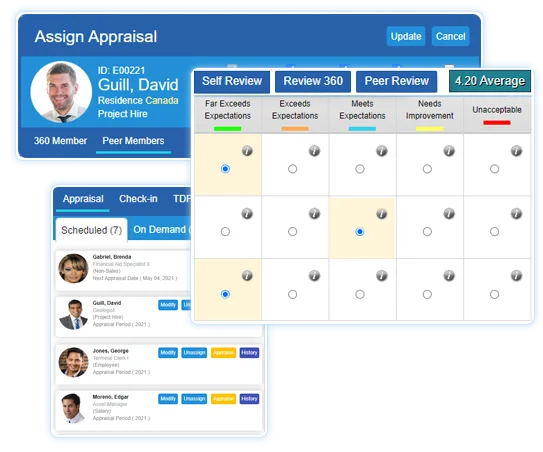
Recognition & Rewards
Employee recognition has been shown to drive engagement, boost productivity, lower turnover, and improve employee well-being and organizational culture. Compliment other engagement initiatives with a social recognition system that encourages managers and employees to give each other positive feedback.
Key Features
- Collaborative communication through posts with configurable groups of employees
- Use library of images to recognize or reward anyone in the organization
- Automatic recognition for birthdays and years of service
- Budget reward points to managers
- Manager can assign reward points for recognized achievement
- Monetize rewards for employees to redeem
- Internal custom redemption catalog or link to third party fulfillment provider
- Generate detailed reports and graphs
Learn More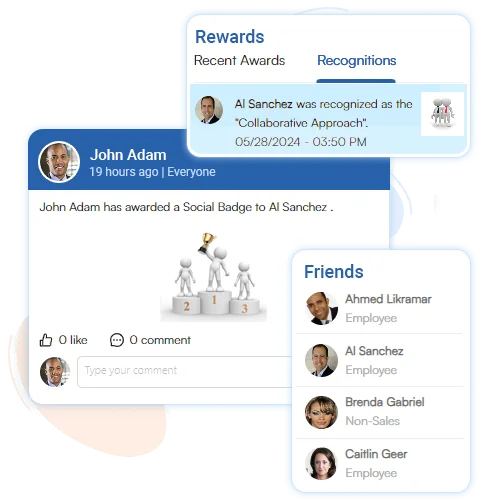
Talent Development Platform - Base
Create a culture of development with Check-Ins, Performance Management, Recognition, Goals, Teams & Talent Development Plans
Engagement Survey
Use Surveys and Action Plans to listen to employees and improve the employee experience
Bullseye Survey
Create & deploy surveys in minutes. Comprehensive reporting with real-time dashboard
Succession Planning
Identify key talent and facilitate internal mobility decisions.
AI Coach
Real-time coaching that helps managers lead better.
AI Advisor
Real-time insights into succession risks and coverage for critical positions
Compensation Planning
Make informed, timely decisions about compensation
Talent Match
How do you know that someone is the right candidate for the job?
Ethics Lifeline
Gives you an outlet to voice your concerns
Workforce Planning
Plan organizational development initiatives with flexible modeling tools
Executive / Human Capital
BI DashboardGain real-time insight into key human capital analytics & metrics
Operational BI Dashboards
Facilitate data-driven decision making with configurable BI dashboards
Bullseye OKRs
Collaborative and measurable goal-setting
Training Management
Track of learning and training progress in a single interface
Competency Management
Build long-term success of your organization
Performance Management
Fully configurable appraisal criteria and choice of rating scales
Recognition & Rewards
Facilitate peer-to-peer and manager-employee engagement
-
-
Company
About Us
Why Bullseye
Technology Partners
Consultants
Strategic Partners
Advisors
Career Opportunities
FAQs
- Our Values
-
Resources
Podcast
Case Studies
Events & Webinars
Recent News
Useful Insights / Links
Testimonials
Blogs
Newsletter Archives
- Data Security
- Contact